
What is Negative SEO?
Negative SEO is a set of malicious actions aimed at reducing the ranking and visibility of your website in search engine results.
Those responsible for these misdeeds are often individuals paid by your competitors who attempt to push rival websites out of the SERPs.
While the implementation of some Negative SEO (On-Page) operations requires the intervention of hacking experts to “change” your web pages, others can be implemented using Off-Page techniques, and therefore operating outside the victim's site.
In this article, you will learn how to protect your Joomla website from one of the most potentially harmful Off-Page attacks: Injection and Parameter Pollution.
Injection and Parameter Pollution
Injection and Parameter Pollution attacks are among the simplest Off-Page attacks to carry out.
In fact, they use backlinks, i.e., URLs to pages on your website, to consume your crawl budget and, in the worst case, associate your domain with query spam.
The crawl budget is the amount of resources (time and capacity) that a search engine dedicates to scanning the pages of a website but, as explained by John Mueller of Google to a user on Reddit, the crawl budget is really only an issue for large sites, i.e. those with more than 10k unique pages.
Crawl budget is really just a problem for massive sites~ John Mueller
So, everything is fine?
No, not at all, because backlinks with spam queries can seriously damage your website's indexing if it doesn't handle the canonical rel tag correctly.
If this tag, which tells search engines what the “canonical” address of your web pages is to be displayed on SERPs, ends up containing unwanted words (e.g., porn, viagra, poker, etc.), then you are a potential victim of a canonical attack!
The damage is inevitable. And it won't be easy to repair!
To carry out a canonical attack thru Injection and Parameter Pollution, all the attacker needs to do is publish links to one or more pages of your website, adding harmful parameters:
www.yoursite.com/your-page?spam=viagra-online
The attack is more malicious if it comes from link farms, that is, from a set of low-quality sites built using black-hat techniques (before) and negative SEO (now), but if the target is a website with fewer than a hundred pages, it can hit and score even with just a few dozen backlinks from non-suspicious sites.
In such a situation, if your pages do not communicate their canonical URL to search engines, they may appear in SERPs in relation to spam queries... or not appear at all because they are blacklisted.
The results would be devastating for your website, products, and brand.
And if you think you're safe because you've configured the canonical rel tag feature on your Joomla site with the core plugin System - SEF, I'm sorry to say that's not the case!
The flaws of Joomla's SEF plugin
Since version 4 of Joomla, there has been a core plugin called “System - SEF.”
This adds SEF support to links in your content and optionally allows you to specify the Site domain parameter.
I quote the description of the parameter:
If your site can be accessed through more than one domain enter the preferred (sometimes referred to as canonical) domain here.
Note: https://example.com and https://www.example.com are different domains.
By using this parameter, the canonical rel tag is inserted into the pages of your website.
Everything seems fine, but in reality, the canonical URL entered is retrieved without performing any routing operations involving scanning the site's navigation tree, but simply by using the URL of the current page as it is (or almost).
This, in addition to not proposing the correct canonical URL in every situation, exposes your website to:
- Duplicate content
- Canonical attack.
Duplicate content
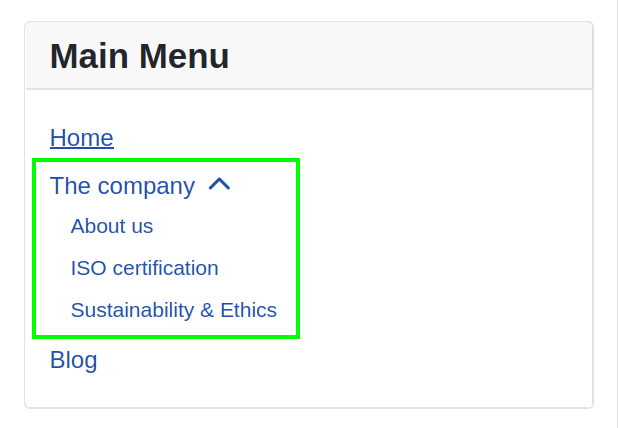
Let's take a simple company website that has three articles describing some important aspects of the company:
- 30 years of experience in innovative technology
- Quality & Management ISO certification
- Daily commitment to sustainability and corporate ethics.
These articles belong to the category The company, which can be accessed from the corresponding menu item.
Below this there are three sub-menu items:
- About us, linked to the article 30 years of experience in innovative technology
- ISO certification, linked to the article Quality & Management ISO certification
- Sustainability & Ethics, linked to the article Daily commitment to sustainability and corporate ethics.
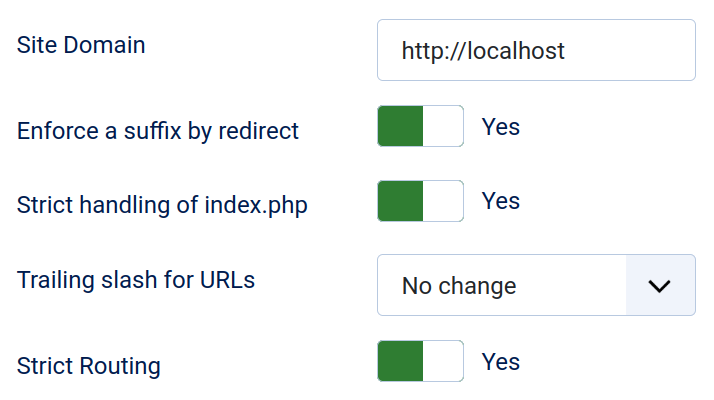
This test website, created with Joomla! 6, runs under Apache on my Linux workstation at
http://localhost/joomla6/
In the System - SEF plugin, I specified the Site Domain and enabled all the routing and redirect features available.
This configuration inserts the canonical rel tag into the website pages and should therefore prevent duplicate content, but in reality it does not.
By visiting the “About us” link and viewing the HTML source of the article, we can see that the canonical rel tag has been inserted, correctly specifying the canonical URL.
http://localhost/joomla6/the-company/about-us
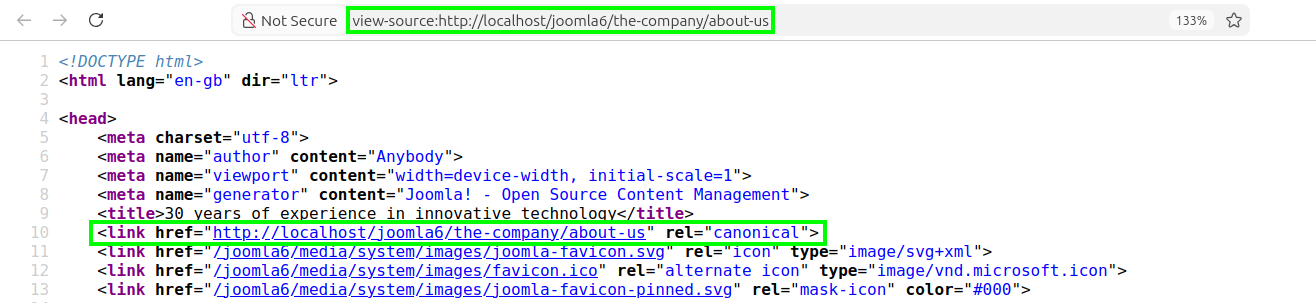
However, you can also view this article by accessing other addresses, such as this one::
http://localhost/joomla6/the-company/30-years-of-experience-in-innovative-technology
Same article, same content. The canonical URL should be the same as that of the “About us” menu item...
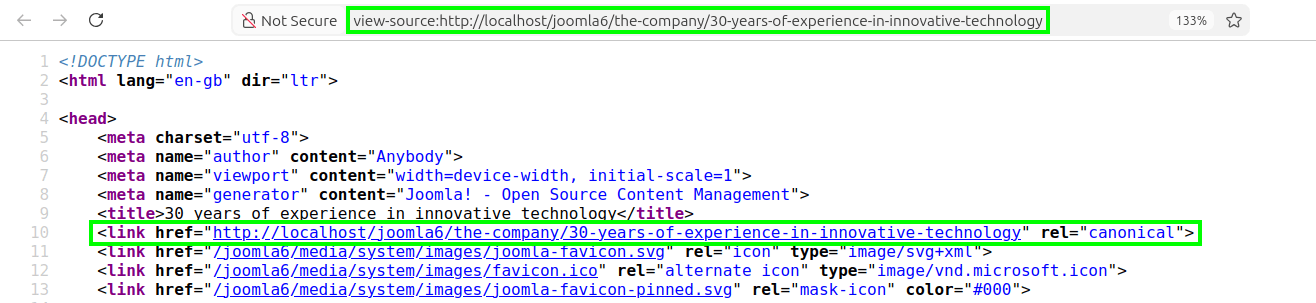
... but as we can see, this is not the case, and this is a problem!
From the perspective of search engines, our website disseminates duplicate content.
This content redundancy could be interpreted as fraudulent practice and lead to penalties on the SERPs of the entire website for keyword stuffing or spam.
And unfortunately, that's not all...
Canonical attack!
As I mentioned in Injection and Parameter Pollution, this type of attack can cause devastating damage, but the most worrying aspect is that a canonical attack can be carried out - and succeed - without any hacking knowledge and without the need to use a link farm.
All the attacker needs is a basic knowledge of HTML, a space on the web where they can link to your website pages, and for your website not to handle the canonical rel tag correctly.
The website I used in the example of duplicate content is a perfect victim, since the Joomla System - SEF plugin does not purge canonical URLs of extra parameters.
This means that you can safely add spam queries to any address on the website and be sure that they will end up in the canonical URL.
Let's type in the address of the “About us” page, adding the extra parameters we have decided to use for our spam.
http://localhost/joomla6/the-company/about-us?daily-discount=viagra+60+pills
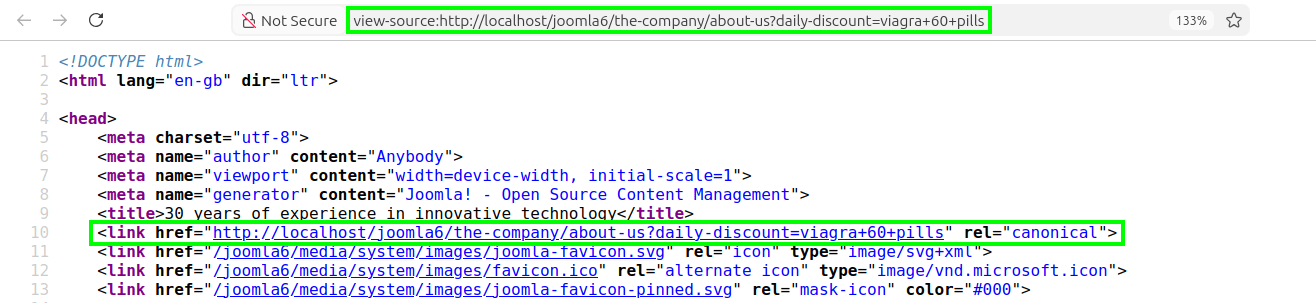
Attack successful!
The unwanted words ended up in the canonical URL that will be read by search engines.
Will the malicious address end up in the SERPs?
It depends on the number of “dirty” links that the attacker manages to spam in relation to the “clean” links on your website.
A knowledgeable user can easily find Python scripts online that automatically post links on social media and blogging platforms.
Forewarned is forearmed...
Correct defects and prevent damage
It seems obvious, but the saying “Better safe than sorry” is more appropriate than ever when it comes to SEO, especially when brand reputation is at stake.
If your website has been the target of a negative SEO attack, recovering from incorrect indexing or getting off a blacklist are not immediate operations... so let's see how to avoid the attack as much as possible.
As you have seen, Joomla's core “System - SEF” plugin is not enough to prevent duplicate content and negative SEO attacks on the canonical URL.
To correct these flaws, I installed our Crusco Canonical URL plugin on the test website mentioned in the previous examples.
This plugin first detects Joomla's SEF configuration, reports the problematic setting, and immediately suggests one of two methods to work around it.
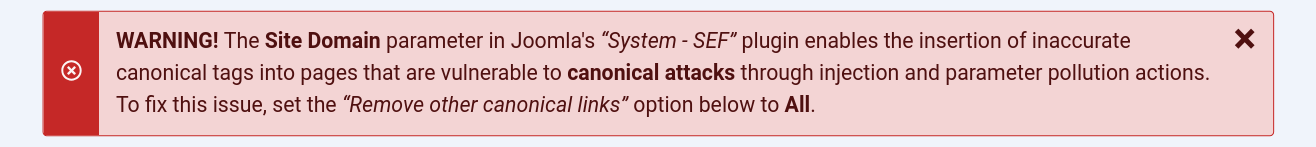
In addition to comprehensive and thorough control over canonical rel tags for the removal of “duplicate content”, Crusco Canonical URL implements three excellent features for effective protection against canonical attacks:
- Spam query filter
- Master malicious search terms
- Custom Canonical URL.
But let's start with the first round: Crusco Canonical URL vs. Duplicate Content.
Saying goodbye to duplicate content
Let's visit the “About us” section once again and take a look at the HTML source code for the article:
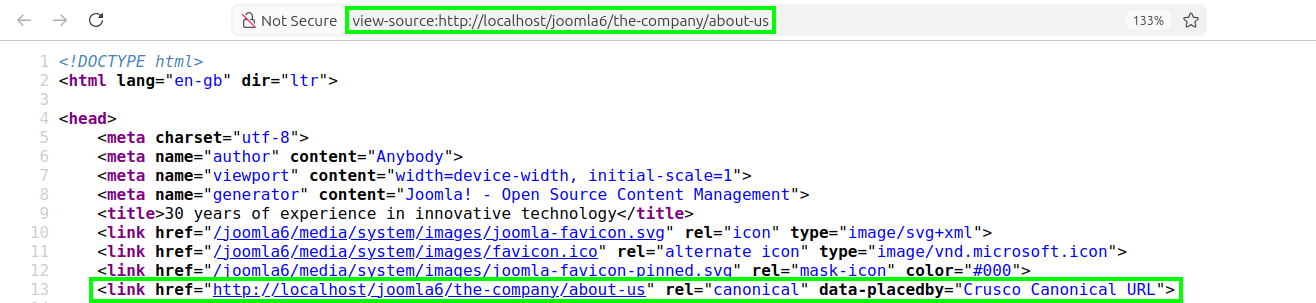
The canonical URL is correct:
http://localhost/joomla6/the-company/about-us
The data-placedby attribute (which can be disabled from the options) tells us that the canonical rel tag was inserted by Crusco Canonical URL.
Now let's access the article from the alternative address:
http://localhost/joomla6/the-company/30-years-of-experience-in-innovative-technology
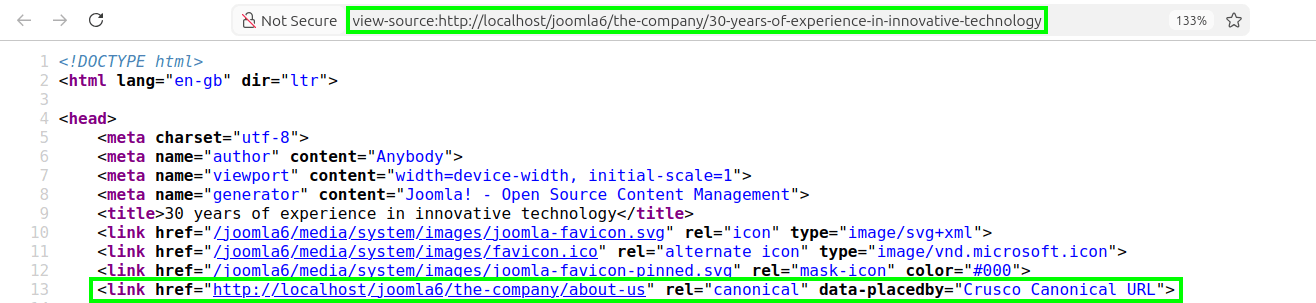
In the HTML source code, we see that the canonical URL of the article has remained the same as the “About us” page, even though it was accessed from a different URL.
This is the correct approach!
We are telling search engines that content accessible from more than one URL should not be considered duplicate content, but rather as resources that always refer to the same page, the one defined by the canonical rel tag.
Next round: Crusco Canonical URL vs. Canonical attack.
Dealing with canonical attacks
As mentioned above, Crusco Canonical URL has three features to defend Joomla websites from “canonical attacks”:- Spam query filter
- Master malicious search terms
- Custom Canonical URL.
Let's check how they work on the usual test website.
Spam query filter
Let's add our spam query to the address of the “About us” page and check the HTML source again.
http://localhost/joomla6/the-company/about-us?daily-discount=viagra+60+pills
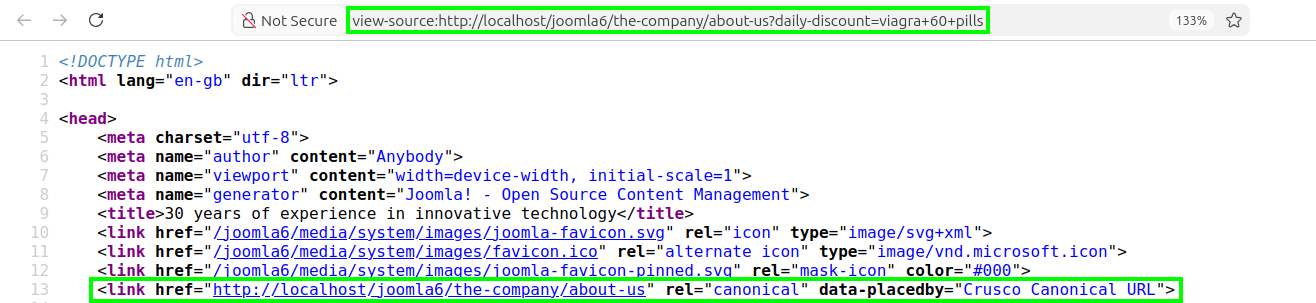
Crusco Canonical URL identified the extra parameters used for spam and removed them from the canonical URL.
The spam query filter worked correctly!
Be aware, however, that this type of attack can also be carried out without using extra parameters, but by exploiting spam injection via permitted text parameters, such as a search query.
Master malicious search terms
Any query made in a website's internal search engine causes the search terms to appear in the address of the search page itself and also in the canonical URL.
On our test website, we create a Smart Search -> Search and start a search for “certification.”
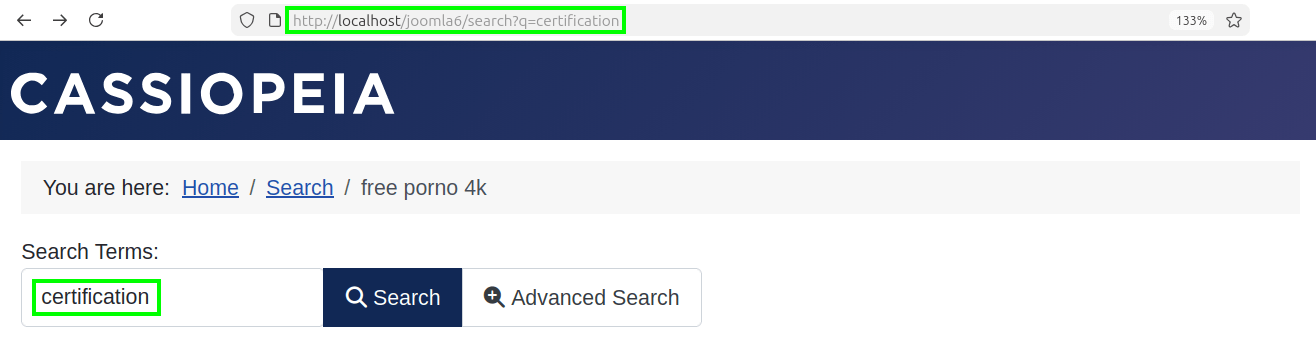
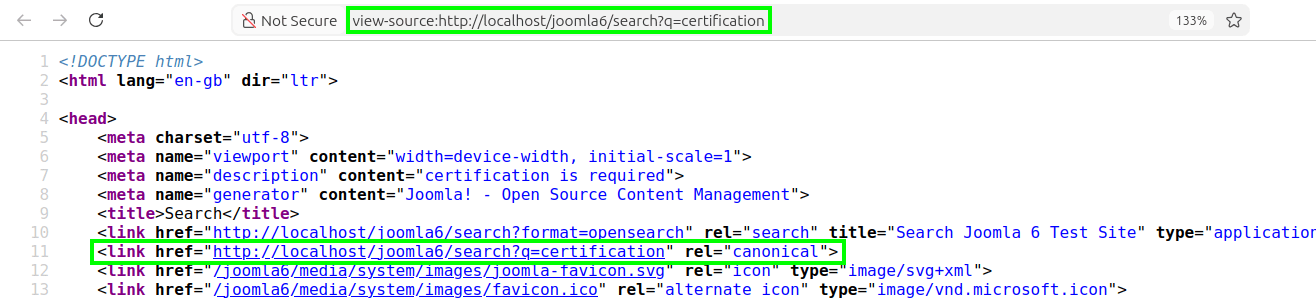
The search page is dynamic: it can return different results and content.
It is therefore correct that the canonical URL changes and that it does so precisely because of the search terms.
Anyone involved in professional SEO is familiar with this behavior and knows exactly how to exploit it to position “targeted” search pages for specific keywords on SERPs.
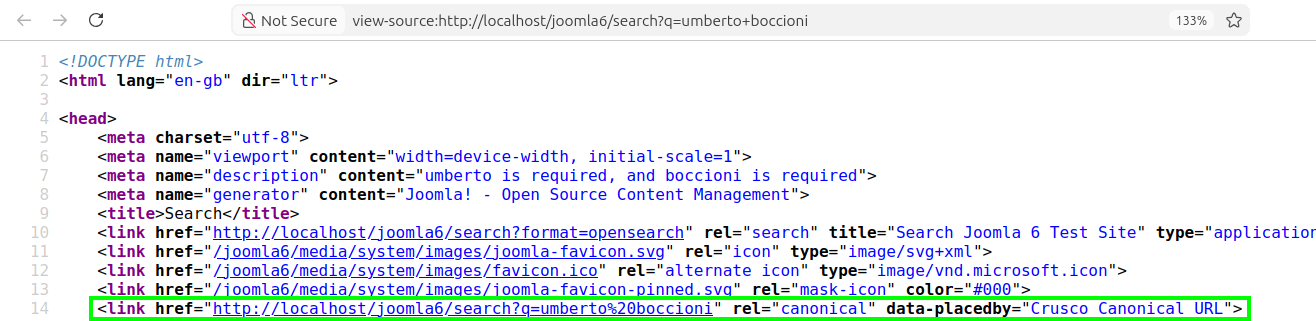
For example, if Google Trends reports a significant increase in searches for the painter (and sculptor) “Umberto Boccioni” and your website has accumulated several articles on this artist over time, it will be very useful to quickly prepare a page that groups these articles together.
The page is good to go:
http://localhost/joomla6/search?q=umberto+boccioni
At this point, all that remains is to submit it to search engines and perhaps pass it on to one of our partners/referrals who will link it on social media, in articles, guest posts, etc.
Everything is looking good, but what if this opportunity is also taken advantage of by the bad guys and not just your SEO specialist?
The search query parameter is an ideal vector for spam injection, and dozens of links like this one
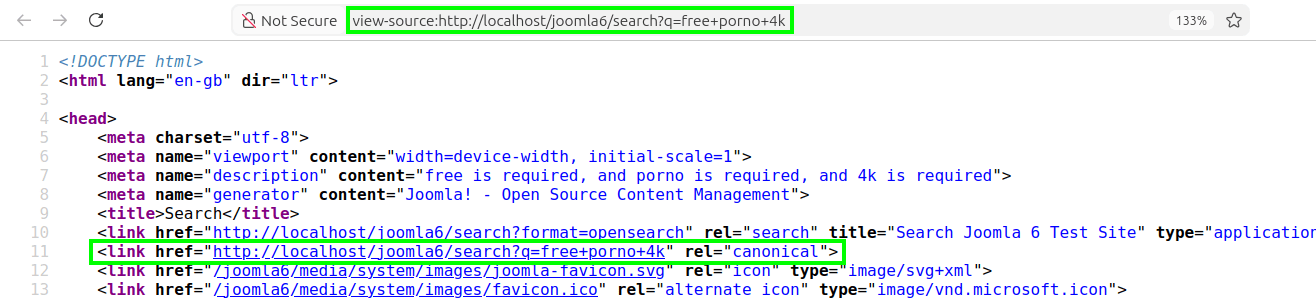
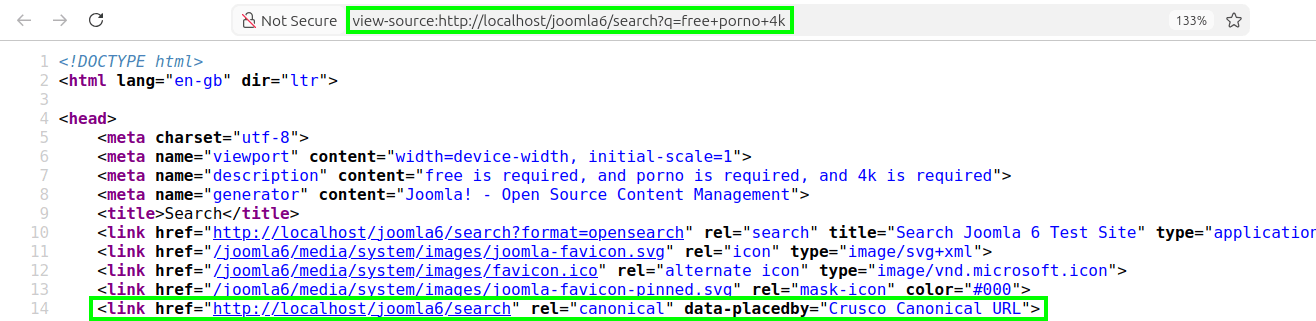
http://localhost/joomla6/search?q=free+porno+4k
may be enough to successfully carry out a “canonical attack.”
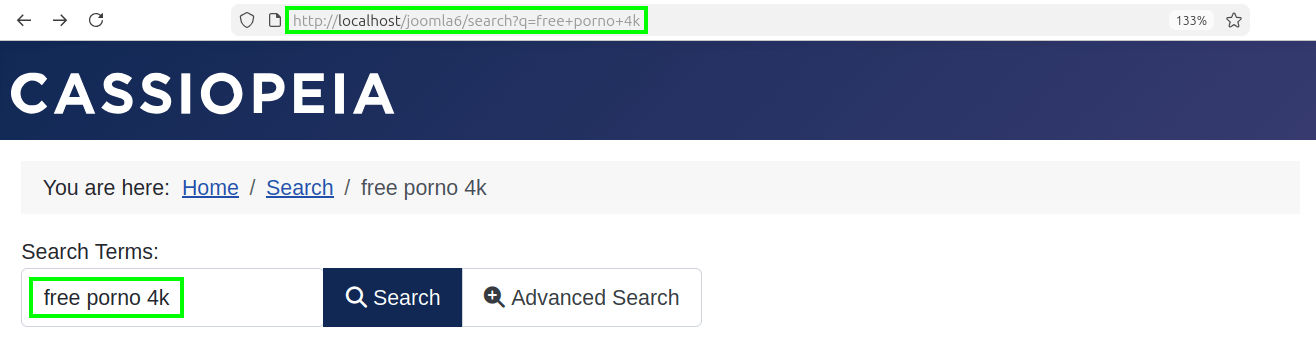
Thankfully, the Crusco Canonical URL plugin allows you to get around this type of attack by offering full control over the terms that end up in the canonical URL of search pages:
- Ignore all search terms
- Ignore all search terms except those specified
- Allows all search terms
- Allows all search terms except those containing unwanted words.
Now let's fix the cases mentioned above on the test website.
The goal is to allow the words “umberto boccioni” in the canonical URL and ignore those from spam injection.
With Crusco Canonical URL, you can achieve this goal in two ways, depending on how you intend to expose your “search” pages to search engines:
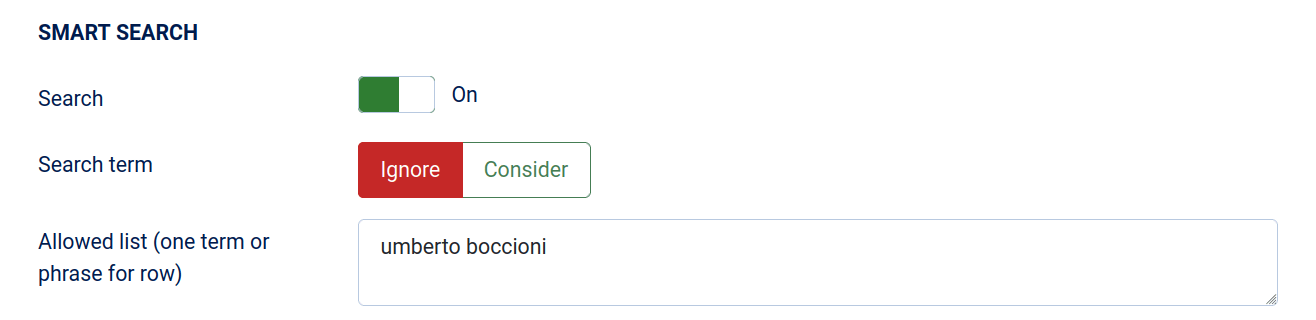
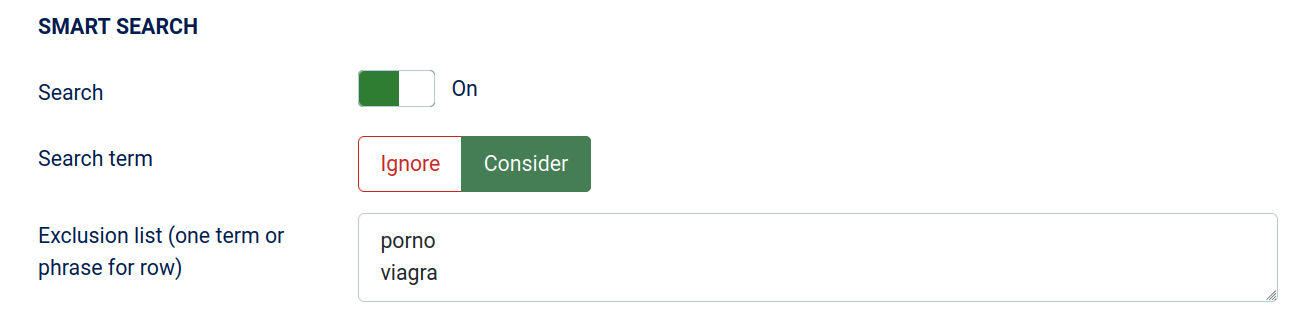
For this example, we chose “Method 1” and, as you can see from the HTML source code, the results are as expected:
allow indexing only of search pages targeted for the chosen keywords, and block all others to prevent a “canonical attack” perpetrated through spam injection in search terms.
Custom Canonical URL
In the unfortunate event that the perpetrator of the attack on your website manages to find a way to bypass the spam filters in a page's canonical URL, Crusco Canonical URL also allows you to manually enter the canonical URL and thus immediately get yourself safe.
This override prevents any spam injection attacks and spam queries, as the canonical URL entered in the canonical rel tag will be exactly the one you specified.
Let's assume that the weak-page has been attacked, and that its canonical URL on the SERPs is now
http://localhost/joomla6/weak-page?compromised=whateverspam
To correct this situation, simply enter a custom canonical URL for that page
http://localhost/joomla6/weak-page
and immediately report the change using the appropriate search engine tool (e.g., Google Search Console).
The search engine crawler will visit your page to scan the changes and acquire the correct canonical URL.
Final thoughts
In this article, you have seen how easy it is for any knowledgeable user to perform malicious actions to undermine a website's SEO ranking.
By applying the Injection and Parameter Pollution technique, it is possible to carry out an Off-Page Negative SEO attack that can cause serious damage to the victim's website if it does not correctly implement the canonical rel tag.
The one inserted by Joomla's core plugin “System - SEF” does not completely eliminate the problem of duplicate content and does not apply any spam injection control on URL parameters exposing your website to this type of attack.
The malicious actor can thus perpetrate and carry out a “canonical attack” with devastating consequences for positioning on SERPs, products, and brands.
We have proposed and shown you our solution: Crusco Canonical URL.
It is a plugin developed by us that improves Joomla's “SEF System” by eliminating the hassle of duplicate content and offering three features for protection against canonical attacks.
Let the level up be with you!

